|
Hey Kaitlyn, Joseph here. We published this in-depth article late on Friday, so I wanted to make sure you saw it today. For months, cybersecurity firm Mandiant has been tracking the hacker behind those massive Snowflake breaches. Ticketmaster, AT&T, Lending Tree, and many more. Now the walls are closing in on this hacker—authorities in Ukraine seized their servers, and Mandiant has a mass of the hacker's Telegram communications. The full story follows below. Judische, a hacker who often has an anime profile picture on one of their many Telegram accounts, has made around $2 million by stealing data from companies and extorting them, he told me on Thursday. Earlier this year, Judische went on a hacking rampage by breaking into instances of Snowflake, a data warehousing tool, and lifting masses of sensitive information. He may have hacked up to 165 companies, including Ticketmaster, Lending Tree, and Neiman Marcus. The breaches have caused chaos across multiple industries, with Judische sometimes publishing data when the companies have not paid up. He even wanted to extort the Drug Enforcement Administration (DEA) with data he stole from pharma giant Bausch Health, according to chat logs I obtained.
This segment is a paid ad. If you’re interested in advertising, let's talk.

Although GenAI technologies drive innovation, they also attract bad actors—child predators, terrorist organizations, and hate groups—who are exploiting these tools for malicious purposes.
To help companies combat these threats, ActiveFence is hosting an upcoming webinar, Designing Your AI Safety Tool Stack: What to Build, Buy, and Blend, featuring Frost & Sullivan’s Global Vice President & AI Program Leader, Nishchal Khorana.
Together, we will break down the key elements of a secure AI safety tool stack—including analytics, incident management, prompt filtering, and red teaming. Attendees will also learn which tools are best built in-house, bought from specialized vendors, and when a hybrid approach is the most effective.
Whether building from scratch or optimizing existing systems, this webinar will help you make informed decisions and ensure the safe, responsible use of AI tech. Register now.
In his typical blackmail attempts, Judische would contact the victim company, sometimes with the help of an intermediary, and offer to produce a video proving he deleted the stolen data in exchange for a hefty payment. If the company didn’t comply, Judische or others would dump the data online, making it publicly accessible. But Judische often made terrible mistakes in those videos. In at least one case, the video showed his system’s hostname, which is basically how the computer identifies itself on a network. Armed with that information, Austin Larsen, a senior threat analyst with cybersecurity company Mandiant, identified where the server hosting some of Judische’s data was. Larsen provided information to relevant parties, they took down the server, which delayed Judische from publishing a victim’s stolen data, Larsen said. Larsen believes he has formed a picture of the sort of person Judische may be, and where the hacker is located broadly. Larsen will present much of his findings at the cybersecurity conference LABScon in Arizona on Friday. Information about Judische’s alleged location has also already trickled out via the media. With the intense investigatory interest in Judische, actions taken against his infrastructure, and Mandiant coordinating with both U.S. and international law enforcement, the walls are closing in on a hacker responsible for some of the most high profile data breaches in recent years. “MANDIANT IS STALKING ME”In some ways, the breaches of Snowflake—which is a platform companies use to store mountains of data—were very simple. Judische took Snowflake credentials harvested by infostealers, which is a class of malware that lifts passwords and other data from infected computers, and used those to login and steal data from companies stored on Snowflake servers. But the hacks’ impact greatly outweighed their simplicity. One of the most significant Snowflake breaches, which Judische worked on with another hacker called John Binns according to Larsen, was the theft of cell and text records on nearly all of AT&T’s customers in April. That data showed what other phone numbers a customer had interacted with, providing a rich picture of someone’s life. Judische told me he met Binns, who has a talent for navigating telecommunications networks, through SIM swapping years earlier. This is where hackers take over a target’s phone number and use that access to then break into online accounts. Both Binns and Judische are part of the broad criminal phenomenon known as the Com, short for Community. Here, thousands of young, typically English-speaking people on Telegram and Discord engage in hacking, fraud, and scams, both against unsuspecting targets and one another. Many members also carry out physical violence, such as assaults, kidnappings, shootings, brickings, and robberies. Com also has some overlap with the nexus of cybercrime activity that security researchers have called Scattered Spider. 💡 Do you know anything else about this case? I would love to hear from you. Using a non-work device, you can message me securely on Signal at +44 20 8133 5190. Otherwise, send me an email at joseph@404media.co. When Binns obtained the AT&T data, he looked up the numbers of rivals inside the Com, as well as the phone numbers of investigators assigned to investigate them, Larsen said. I obtained a subset of the AT&T data which corroborates this. “This is really an escalation,” Larsen said. Before, Binns and Judische may have been focused on getting money. Or in Binns’s case, he wrote manifestos and other documents railing against the U.S. government. Now at least one of them was performing counter-espionage with access to a staggeringly sensitive dataset. After this breach, Binns was arrested in Turkey. Binns’s federal public defender in the U.S., Greg Murphy, told me he has “not been able to communicate with Mr. Binns, despite many efforts. One challenge is that the consulate will not help me speak to Mr. Binns unless I provide a signed privacy act waiver, which of course would require that I speak to him.”
With his partner out of the picture, Judische compromised more companies’ Snowflake instances. He has used a dizzying array of usernames and handles. According to Larsen, they included zfa, catgwuirrel, scarlet, ddd, crwdstrke, terracotta childsoldier, and many more. Others are Waifu and Catist. Judische’s post style is erratic, with long strings of staccato messages. He also does what people in Com refer to as “detrace,” which is accusing other people of breaches in an attempt to throw security researchers or investigators off. In some messages he makes physical threats to researchers and other people. “ill have someone blowtorched <REDACTED> into their back to demonstrate to <REDACTED> first,” Judische said in one redacted message that Mandiant provided to me. Over the next few months, accounts on the crime-focused forum Breached announced a series of new hacks, including of Ticketmaster, which contained data that could be used to generate tickets for certain concerts. That later included Taylor Swift Eras tour barcodes too. Other victims included Neiman Marcus, Lending Tree, and Advance Auto. According to Larsen, all of these breaches were Judische’s work. Mandiant said in a June blog post that Judische—who the company code-named “UNC5537” in that post—may have breached around 165 different organizations.  A message from Judische. Image: 404 Media. During this time, Larsen said he read all of Judische’s public Telegram messages. Day in, day out, Larsen sat in front of the tsunami of texts, looking for clues that could narrow down Judische’s identity or reveal a way to disrupt him. Judische, it seemed, suspected that the cybersecurity world was watching him. “Mandiant are stalking me,” Judische wrote in one crime-focused Telegram group. “They have several ppl … in this chat.” Larsen said it was jarring to be scrolling through Judische’s messages, and then suddenly see a message calling out his employer. Larsen saw one of those texts just a few minutes after Judische posted it, as if he was following Judische’s shadow around a corner into an alley. Over the course of months, Larsen said he obtained many of Judische’s Telegram private messages. Larsen declined to say where he got these from, but Vinny Troia, a security researcher who has controversially advertised data on crime forums according to previous reporting, told me he was “working” with Larsen. Troia has acted as a proxy between Judische and companies he has attempted to extort, according to direct messages I obtained that Troia sent to a source. In some of the leaked text messages, Troia also appears to encourage the source, who is an associate of Judische’s, to hunt for more data. “I have an idea on making you some money,” Troia texted to the source, discussing another data breach. Troia told the source he was offering to help Judische by structuring the stolen data to then take to victim companies. “I am literally offering to piece it together for him,” Troia wrote. “He is easily looking at a 10m [$10 million] payday on this. If you can help push things along I can get him to give you some money.” Regarding data stolen from Lending Tree, Troia wrote that Judische “is sitting on another huge possible goldmine with the lending tree data but he won’t take a minute to either merge it or send it to me to do it for him.” Troia adds he “did it for Neiman,” in a direct message to the source under his own name. 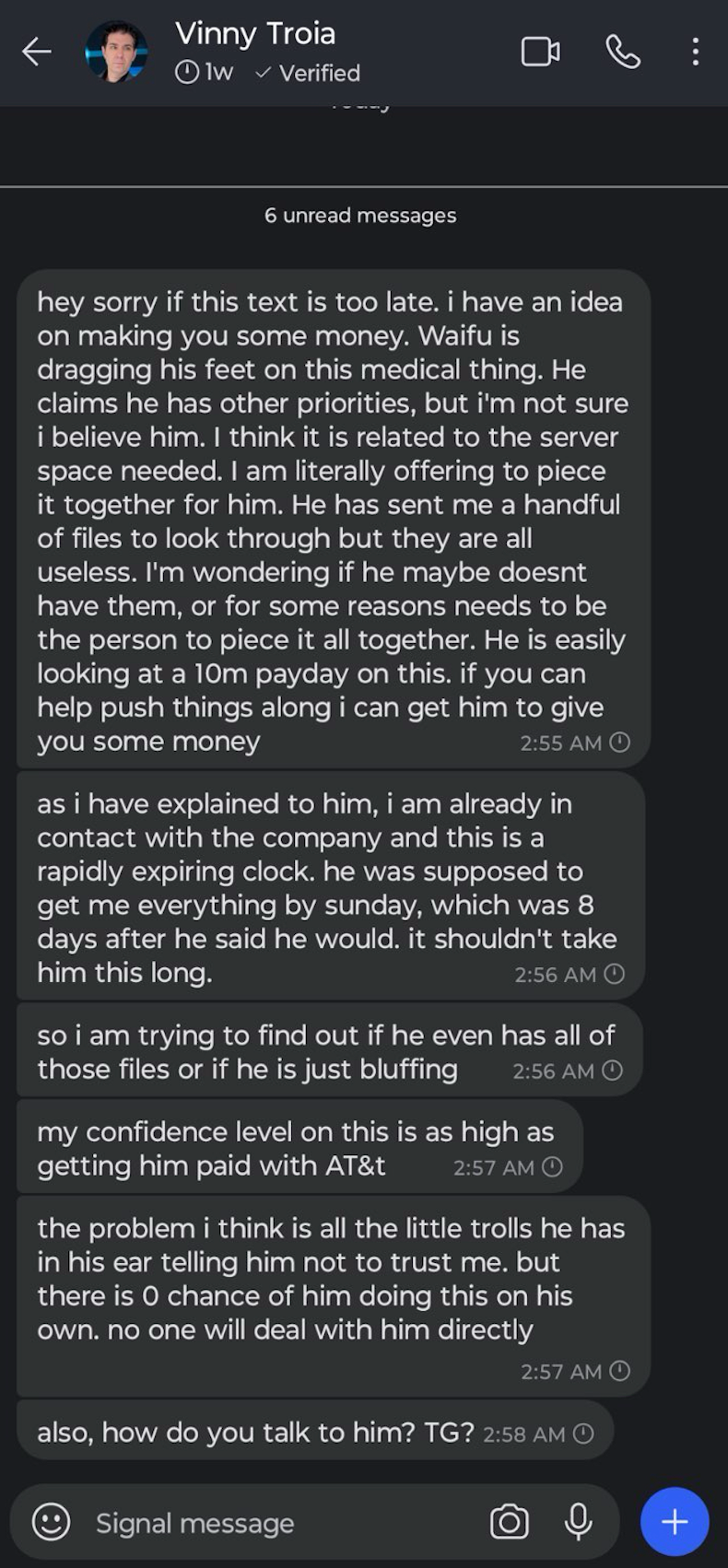 A screenshot of a text message sent by Vinny Troia. Image: 404 Media. WIRED previously reported that AT&T paid the hackers $370,000 to delete the stolen data. In another message I obtained, Troia said that if the source could access Binns’s servers in Turkey, which he believed could still contain AT&T data, “I can probably get you money from AT&T for that.” He also asked the source “what if you went there and just grabbed the servers and took them back with you.” He also offered to buy data from the source from another hacked telecom, according to another message. When I contacted Troia for comment in July, he repeatedly tried to call my source. “Call me. Stop being a pussy,” he also texted the source, according to a screenshot of the message. Troia told me he has not done anything illegal while investigating Judische. Regarding asking to buy data from another hacked telecom, Troia said “sometimes I tell people things just to keep them talking. I haven’t actually purchased anything.” When I sent a screenshot of the text message to Troia in which he discusses the idea for making my source some money, Troia’s offers to Judische to piece together data, and asking my source to “push things along,” Troia told me “you say what you need to so they keep talking.” In one email, Troia told me “I offer my services free of charge. I don’t receive any money and can prove this.” Then in another email, Troia said “My fee is industry standard.” It is not clear why Troia said both that he does the work for free and that his fee is industry standard. DISRUPTING JUDISCHEOn top of access to many of the hacker’s communications, Larsen said Mandiant also has three hundred “indicators” related to Judische. Because Mandiant is also often working the incident response to Judische’s breaches, in which the company comes in to figure out what happened, that means Mandiant gathers data such as what IP address Judische used to steal any data. Larsen can see Judische’s footprints across different breaches. With that “firehose” of chats and other data, and “hundreds of hours” of his time as well as work from other teams at Mandiant, Larsen thinks he’s built a pretty good—or “moderate confidence”—profile of the sort of person Judische is. A male in his 20s. Probably in Canada. Has an interest in video games, geopolitics, and catgirls. And when Judische is in the middle of an intrusion, he can potentially stay up for days on Telegram with little sleep, Larsen said. Judische’s motivations, according to Larsen are “money and notoriety.” In one message I saw Judische posted to a Telegram group chat, he said “I remember almost breaking my hand punching my monitor when I made only 70k in 1 night in like 2019.” “I do like catgirls, this much is true,” Judische told me, when I asked for comment in response to Mandiant’s findings. “Geopolitics is boring this is only for larping as a defense official, which is usually for the purpose of mocking the use of HUMINT [human intelligence] on part of the FBI/DHS taskforce.” Judische’s messages are often rambly like this, including acronyms and names of random companies. Part of Larsen’s job has been filtering out the truth from the fiction, in part by investigating the intrusions themselves. “I usually tell ppl I'm a girl from various cities in Ontario or Quebec, and sometimes Germany. Most of the things ‘Waifu’ says to ppl about ‘Waifu’ are either blatant trolling or intentional misdirection,” Judische added when asked for comment, referring to one of his earlier handles. Despite some of the clear attempts at misinformation from Judsiche, “what we've found is there is truth in a good amount of what they say,” Larsen said. While Judische told me he had made just under $2 million dollars from Snowflake-related extortions, Mandiant put Judische’s earnings since April at around $3 million.  A message from Judische describing Troia. Image: 404 Media. In the June blog post about Judsiche’s approximately 165 victims, Mandiant said that Judische used servers from Alexhost SRL, a company in Moldova. After publication of that post, Judische then moved his infrastructure to providers in Ukraine, Larsen said. Larsen discovered this because of one of Judische’s mistakes. In one deletion video, Judische showed their hostname, “Administrator@WIN-DLBSJ534840.” Larsen said he then used the computer search engine Censys to find the IP addresses of those hosts and track down Judische’s infrastructure to Ukraine. Larsen says this infrastructure was then taken down. What followed was Judische sending a flurry of more than 200 messages on Telegram, Larsen said. Some of these were in public Telegram groups. At the time I saw Judische blame the SBU, the Security Service of Ukraine, for the disruption. Judische was “definitely frustrated,” Larsen said. Initially when I asked about Ukrainian authorities seizing his server, Judische deflected, saying “the issue is resolved. It was a miscommunication and they brought the machine back. It has nothing do with snowflake either it’s to do with trickbot,” referring to a famous piece of malware. Later, when he posted about authorities apparently seizing a server again, Judische sent me a screenshot of an email allegedly from the web host. “We received a request from the law enforcement agency of Ukraine with information about the illegal use of the server at the IP address (including for the distribution and use of malicious software),” it reads. “At the same time, the service agreement provides for the termination of services and the retention of data in the event of the distribution and use of malicious software.” “Yeah they did lol,” Judsiche said when I asked if Ukrainian authorities seized one of his servers. “They r so annoying.” He also claimed that Telegram has deleted at least one of his accounts. Larsen said Mandiant has coordinated with both U.S. and international law enforcement, but Mandiant declined to say whether the company has given the authorities Judische’s suspected real identity. The Royal Canadian Mounted Police (RCMP) declined to comment on whether it is aware of Judische allegedly being in Canada, or whether it has communicated with U.S. law enforcement about this hacker. “The RCMP does not generally confirm or deny investigations unless criminal charges are laid,” a spokesperson said. The FBI declined to comment.
|